Client Need
Our client, an insurance company, was aware that a significant number of users who purchase insurance from their website tampered with their application in order to be able to successfully purchase an insurance policy.
Our Solution
We proposed and implemented Acoustic Experience Analytics (Tealeaf) for them as our solution. Now, having identified multiple suspect purchase indicators, they can detect potential suspect purchases and save recorded sessions of such purchases that they can use as proof if required to take necessary action.
The Benefits
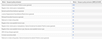
SUSPECT POLICY PURCHASES
We discovered that around 10% of users engaged in various kinds of manipulation in order to be able to successfully purchase an insurance policy. This included:
- Price manipulation
A visitor modifies any answers that resulted in lower premium amounts. For example, one customer initially answered ‘yes’ to a question asking whether they have previously submitted an insurance claim, only to later change it to ‘no’ when asked for more details about the claim.
- Refused insurance
Due to the company’s underwriting criteria, visitors who were refused insurance were able to restart the application and answer the initial questions differently to be accepted into a policy. For example, one customer initially confirmed that their license had been suspended previously and were promptly denied a policy. To successfully – and fraudulently – obtain a policy, they went back in the application and changed their answer to indicate that it had never been suspended.
In total, 26 such suspect policy purchase indicators are now being detected. Now, if somebody changes an answer to lie on their application, it can be detected – and prevented.
AUTOMATED TRACKING OF SUSPECT POLICIES
An integral feature of Tealeaf Data Export. We configured a scheduling task that automatically extracts all session data (replays and digital interaction data) of these suspect policy purchases and are stored on a cloud object storage which the insurance company accesses using an S3 compliant tool.
The customer uses this data exported from Tealeaf to update their internal CRM and Databases and flag these suspect purchases, giving their fraud investigators a head start who can easily access all information relating to these purchases.